A new report published by cybersecurity researchers has unveiled evidence of Iranian state-sponsored hackers targeting dozens of companies and organizations in Israel and around the world over the past three years.
Dubbed “Fox Kitten,” the cyber-espionage campaign is said to have been directed at companies from the IT, telecommunication, oil and gas, aviation, government, and security sectors.
“We estimate the campaign revealed in this report to be among Iran’s most continuous and comprehensive campaigns revealed until now,” ClearSky researchers said.
“The revealed campaign was used as a reconnaissance infrastructure; however, it can also be used as a platform for spreading and activating destructive malware such as ZeroCleare and Dustman.”
Tying the activities to threat groups APT33, APT34, and APT39, the offensive — conducted using a mix of open source and self-developed tools — also facilitated the groups to steal sensitive information and employ supply-chain attacks to target additional organizations, the researchers said.
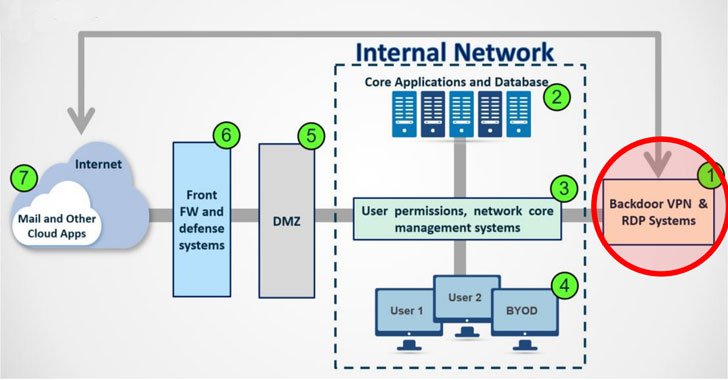
Exploiting VPN Flaws to Compromise Enterprise Networks
The primary attack vector employed by the Iranian groups has been the exploitation of…
http://feedproxy.google.com/~r/TheHackersNews/~3/7XVBn0UzKZ0/iranian-hackers-vpn-vulnerabilities.html
