Popular video conferencing app Zoom has addressed several security vulnerabilities, two of which affect its Linux client that could have allowed an attacker with access to a compromised system to read and exfiltrate Zoom user data—and even run stealthy malware as a sub-process of a trusted application.
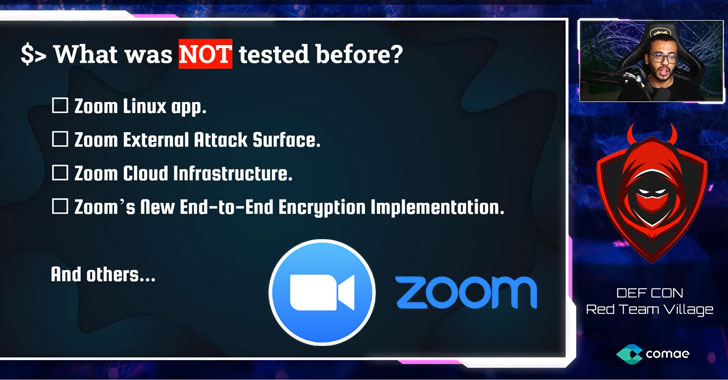
According to cybersecurity researcher Mazin Ahmed, who presented his findings at DEF CON 2020 yesterday, the company also left a misconfigured development instance exposed that wasn’t updated since September 2019, indicating the server could be susceptible to flaws that were left unpatched.
After Ahmed privately reported the issues to Zoom in April and subsequently in July, the company issued a fix on August 3 (version 5.2.4).

It’s worth noting that for some of these attacks to happen, an attacker would need to have already compromised the victim’s device by other means. But that doesn’t take away the significance of the flaws.
In one scenario, Ahmed uncovered an issue with the Zoom Launcher for Linux that could allow an adversary to run unauthorized software owing to the manner it launches the “zoom” executable.
“This…
http://feedproxy.google.com/~r/TheHackersNews/~3/5X4byI1leOQ/zoom-software-vulnerabilities.html
