A prolific North Korean state-sponsored hacking group has been tied to a new ongoing espionage campaign aimed at exfiltrating sensitive information from organizations in the defense industry.
Attributing the attacks with high confidence to the Lazarus Group, the new findings from Kaspersky signal an expansion of the APT actor’s tactics by going beyond the usual gamut of financially-motivated crimes to fund the cash-strapped regime.
This broadening of its strategic interests happened in early 2020 by leveraging a tool called ThreatNeedle, researchers Vyacheslav Kopeytsev and Seongsu Park said in a Thursday write-up.
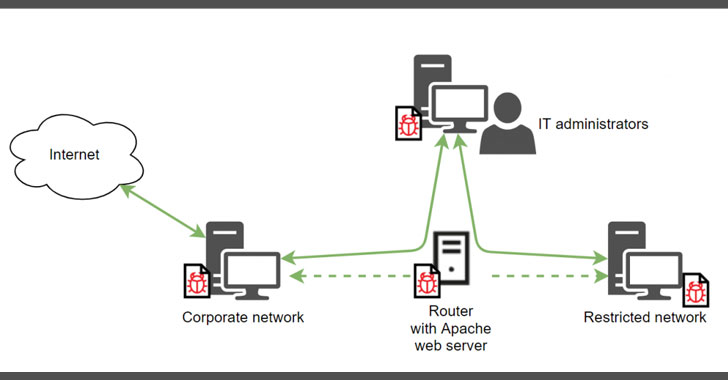
At a high level, the campaign leverages a multi-step approach that begins with a carefully crafted spear-phishing attack leading eventually to the attackers gaining remote control over the devices.
ThreatNeedle is delivered to targets via COVID-themed emails with malicious Microsoft Word attachments as initial infection vectors that, when opened, run a macro containing malicious code designed to download and execute additional payloads on the infected system.
The next-stage malware functions by embedding its malicious capabilities inside a Windows backdoor that…
http://feedproxy.google.com/~r/TheHackersNews/~3/70y1849WSoA/north-korean-hackers-targeting-defense.html
