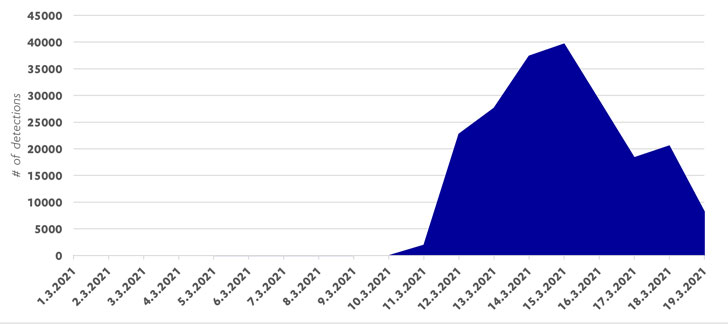
More than a week after Microsoft released a one-click mitigation tool to mitigate cyberattacks targeting on-premises Exchange servers, the company disclosed that patches have been applied to 92% of all internet-facing servers affected by the ProxyLogon vulnerabilities.
The development, a 43% improvement from the previous week, caps off a whirlwind of espionage and malware campaigns that hit thousands of companies worldwide, with as many as 10 advanced persistent threat (APT) groups opportunistically moving quickly to exploit the bugs.
According to telemetry data from RiskIQ, there are roughly 29,966 instances of Microsoft Exchange servers still exposed to attacks, down from 92,072 on March 10.
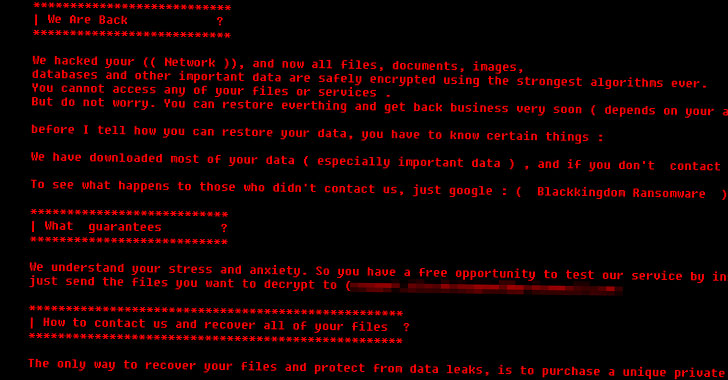
While Exchange servers were under assault by multiple Chinese-linked state-sponsored hacking groups prior to Microsoft’s patch on March 2, the release of public proof-of-concept exploits fanned a feeding frenzy of infections, opening the door for escalating attacks like ransomware and hijacking web shells planted on unpatched Microsoft Exchange servers to deliver cryptominers and other malware.
“To make matters worse, proof-of-concept automated attack scripts are being made publicly…
http://feedproxy.google.com/~r/TheHackersNews/~3/9gpZG_Qu02c/black-kingdom-ransomware-hunting.html
