Cybersecurity researchers are warning of ongoing attacks coordinated by a suspected Chinese-speaking threat actor targeting the Afghanistan government as part of an espionage campaign that may have had its provenance as far back as 2014.
Israeli cybersecurity firm Check Point Research attributed the intrusions to a hacking group tracked under the moniker “IndigoZebra,” with past activity aimed at other central-Asian countries, including Kyrgyzstan and Uzbekistan.
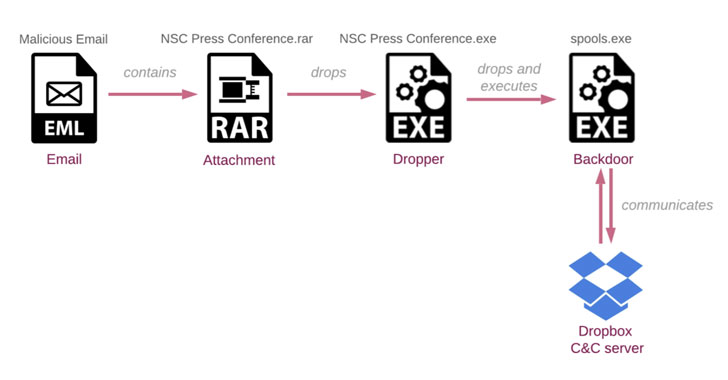
“The threat actors behind the espionage leveraged Dropbox, the popular cloud-storage service, to infiltrate the Afghan National Security Council (NSC),” the researchers said in a technical write-up shared with The Hacker News, adding they “orchestrated a ministry-to-ministry style deception, where an email is sent to a high-profile target from the mailboxes of another high-profile victim.”

IndigoZebra first came to light in August 2017 when Kaspersky detailed a covert operation that singled out former Soviet Republics with a wide swath of malware such as Meterpreter, Poison Ivy RAT, xDown, and a previously undocumented piece of malware called xCaon.
Check Point’s investigation into the attacks commenced in April when…
http://feedproxy.google.com/~r/TheHackersNews/~3/4Y6MHBv-U8A/indigozebra-apt-hacking-campaign.html
